Two aspect authentication (2FA) improves account security by simply requiring an additional method of corroboration when users log in. Rather than just depending on the user’s password, it takes a piece of equipment like an authenticator app or YubiKey to verify the user’s information. This makes sure that only the actual owner of this device can easily log in, even if their credentials are compromised.
Presently, 2FA is needed for publishers with advanced permissions and admins on most projects which is optional for some other types of users (see the section down below on how to allow it). However , any publisher can enhance their account security by enabling two point authentication because of their Wikipedia consideration. This is especially here are the findings advised for facilitators and editors with advanced permissions, especially in mild of a lot of high-profile cracking incidents that contain led to vandalism of the encyclopedia.
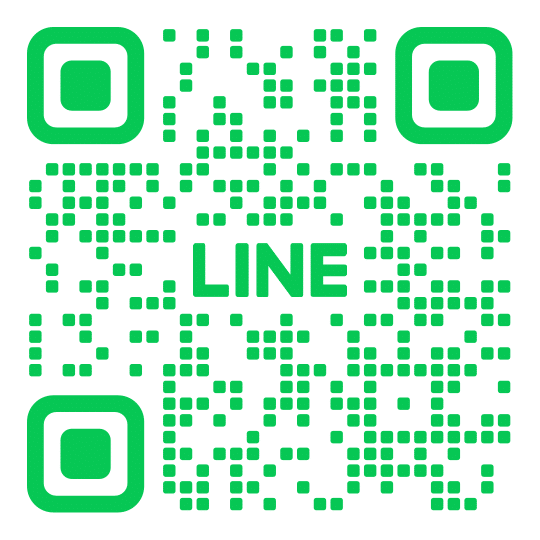
To enable 2FA, click a message in the upper right corner of the personal web page to go to your settings and next select your Multi-Factor Authentication preferences. Then simply, click Permit. Alternatively, an administrator while using Users and Permissions | Manage Two-Factor Authentication Assignments base permission can use a similar page to point that any kind of role that requires 2FA will have to have the user to build 2FA upon their primary login. This kind of setting as well enables managers to specify how often the role will be presented with the 2FA challenge, which works in conjunction with the time of day within the user’s trustworthy device (see Help: Two-Factor Authentication). Users who decide to receive their very own verification programs via TEXT must make sure their smart phone is allowed for txt messaging and they have an authenticator app attached to it.